On March 31, 2026, a routine release of Anthropic’s Claude Code CLI tool exposed what should never have been public: a large (59.8MB) JavaScript source map file embedded in the npm package. The file itself contained the blueprint. Once processed, it allowed reconstruction of significant portions of Claude Code’s internal source.
No hacking required. No credentials stolen. The file was simply there, waiting.
By early morning, Chaofan Shou, a blockchain security researcher, had posted this leak on X with a direct download link, after which the issue gained widespread attention and was widely shared and mirrored online. Repositories -centralized digital storage locations – that hosted the exposed material were rapidly replicated across platforms before takedown efforts began.
Claude code source code has been leaked via a map file in their npm registry!
Code: https://t.co/jBiMoOzt8G pic.twitter.com/rYo5hbvEj8
— Chaofan Shou (@Fried_rice) March 31, 2026
Repositories hosting the leaked code were subsequently taken down following DMCA notices – though the takedown itself became a second misstep. Anthropic’s notices were executed against roughly 8,100 GitHub repositories, including legitimate forks of Anthropic’s own public Claude Code repo.
Boris Cherny, Anthropic’s head of Claude Code, later confirmed the overreach was unintentional and retracted the bulk of the notices.
This was not intentional, we’ve been working with GitHub to fix it. Should be better now.
— Boris Cherny (@bcherny) April 1, 2026
Multiple reports indicate that the source code of its “Claude Code” CLI tool – roughly 500,000 to 512,000 lines of TypeScript across around 1,900 files – was exposed and analyzed by developers within hours. Developer analysis, including insights shared in public threads, suggests that significant portions of Claude Code’s internal architecture, tooling systems, and workflows were revealed through the leak.
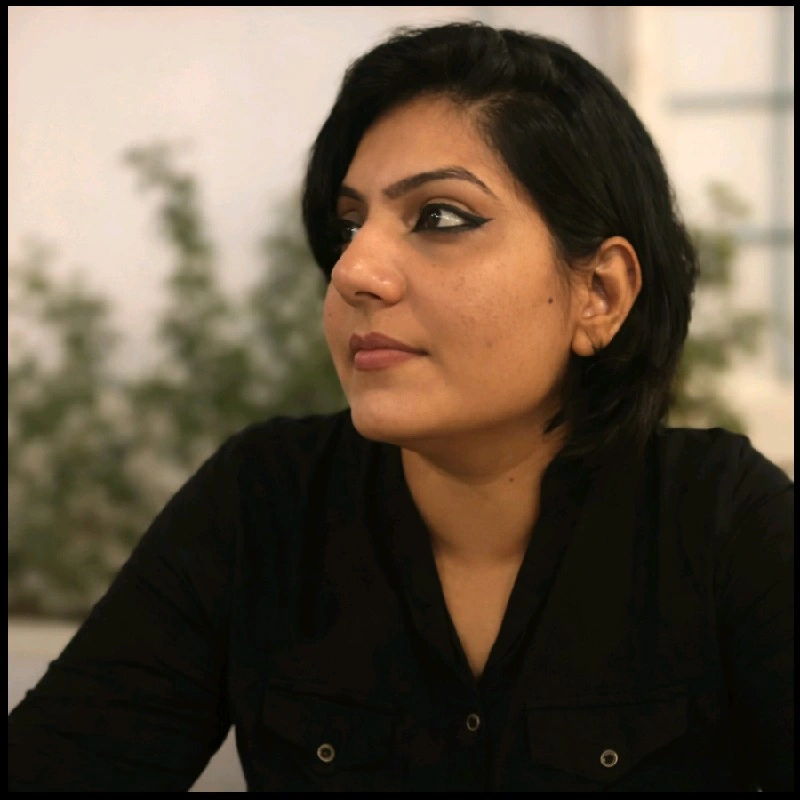
AI FrontPage Asked Anthropic. Here’s What They Said
In a direct response to AI FrontPage editor Pratima O Pareek, Anthropic characterized the incident as operational, not adversarial:
“Earlier yesterday, a Claude Code release included some internal source code. No sensitive customer data or credentials were involved or exposed. This was a release packaging issue caused by human error, not a security breach.”
Anthropic did not provide details on the full scope of the leak, when it was internally identified, or the specific safeguards being introduced.
In a public post on X, Boris Cherny confirmed the leak resulted from human error during a missed manual deployment step, adding that fixes have been implemented and additional safeguards are being introduced.
👋 it was human error. Our deploy process has a few manual steps, and we didn’t do one of the steps correctly. We have landed a few improvements and are digging in to add more sanity checks.
Like with any other incident, the counter-intuitive answer is to solve the problem by…
— Boris Cherny (@bcherny) April 1, 2026
What the Claude Code Leak Revealed About Its Internal Architecture
Developers digging through the code reported finding a feature called KAIROS – referenced over 150 times in the source – described as an autonomous daemon mode that allows Claude Code to operate as a background agent, performing memory consolidation while the user is idle. Separately, internal model codenames were identified: Capybara for a Claude 4 variant, Fennec for Opus, and an unreleased model called Numbat still in testing.
Developers who went through the code described a system built around modular tools, command-based execution, and structured workflows. The picture that emerged was of something far more layered than a chat interface.
Multiple analyses pointed to a range of built-in tools and command-driven capabilities consistent with a production-grade engineering system, though Anthropic has not independently confirmed these specifics.
Boris Cherny also described the incident as a systemic issue, emphasizing that failures stem from process, culture, or infrastructure -not individuals.
Mistakes happen. As a team, the important thing is to recognize it’s never an individuals’s fault — it’s the process, the culture, or the infra.
In this case, there was a manual deploy step that should have been better automated. Our team has made a few improvements to the…
— Boris Cherny (@bcherny) April 1, 2026
Industry Reaction to the Claude Code Leak
The developer community acted fast. Within hours, the exposed code was mirrored, forked, and archived across platforms – spreading way faster than any takedown effort. It’s a familiar lesson: once source code is out in the open, controlling its spread becomes nearly impossible, regardless of what legal or platform-level tools are deployed.
The timing added another layer of concern. Separately, a supply chain attack affecting the Axios npm package was reported during the same timeframe. Developers who installed or updated Claude Code via npm on March 31 between 00:21 and 03:29 UTC may have downloaded a malicious version containing a Remote Access Trojan. No direct connection to the Claude Code incident has been confirmed.
Discussions on DEV Community pointed to packaging oversights, including unintended source map inclusion, as a common way internal code can be exposed without a breach.
Malware Exploitation Following the Claude Code Leak
Zscaler ThreatLabz, the threat intelligence and research division of cybersecurity firm Zscaler, identified a malicious GitHub repository exploiting the Claude Code leak as a lure, masquerading as reconstructed TypeScript source code. The repository’s README claimed the code was rebuilt from the exposed .map file and offered a modified version with “unlocked” enterprise features and no usage limits.
In reality, users who downloaded the archive received ClaudeCode_x64.exe — a Rust-based dropper that installs Vidar v18.7, an information-stealing malware, along with GhostSocks, a tool used to proxy network traffic through infected systems.
The repository surfaced prominently in Google search results for “leaked Claude Code,” underscoring how quickly threat actors moved to capitalize on the incident.
Human Error or System Failure? The Bigger Question Behind the Claude Code Leak
Anthropic has framed the incident as human error. That may be accurate. But the more important question is whether the systems surrounding that human error were designed to catch it – or whether they allowed it to pass unnoticed until the internet found it first.
This is not the first time. A nearly identical source map exposure occurred with an earlier version of Claude Code in February 2025 – raising the question of whether the lessons from that incident were ever fully acted upon
Why the Claude Code Leak Matters for AI Systems and Security
This incident lands at a moment when AI companies are under more scrutiny than ever – not just for what their models do, but for how responsibly they operate behind the scenes.
The code is out. The mirrors remain. While Anthropic has described the incident as human error, the scale and visibility of the leak have raised questions about operational safeguards and trust.
Anthropic’s response to AI FrontPage explains the incident as a release packaging error caused by human error and confirms that no sensitive customer data or credentials were exposed, but leaves key questions unanswered around the scope of the exposure and the safeguards now being put in place.
The Claude Code leak ultimately raises deeper questions about system-level safeguards in AI systems.
Human error explains what happened. It doesn’t explain why the same thing was allowed to happen twice.
Also Read: Anthropic’s Claude Code Security Triggers Selloff in Cybersecurity and Software Stocks